Poly vs OpenClaw (Clawdbot/Moltbot): Why Production-Grade Agentic Ops Requires Governance (v3 — sources updated)
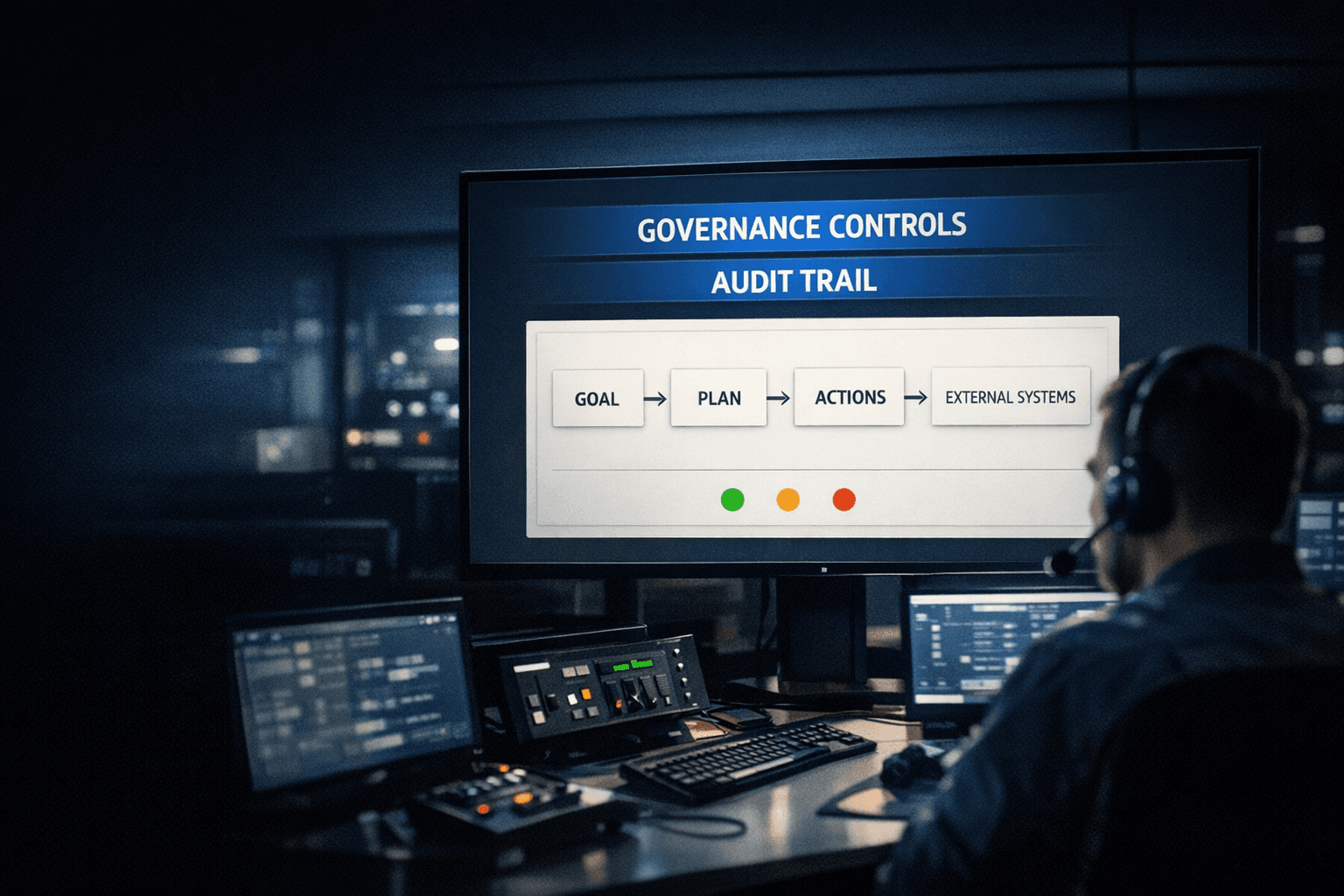
Table Of Content
- TL;DR
- Table of Contents
- What’s happening and why this matters
- What OpenClaw is (and why it’s going viral)
- The two failure modes: security + deployability
- Why this is predictable: agentic expands blast radius
- How Poly positions against this category
- A practical security/ops checklist (non-theoretical)
- Field-ready messaging (no mud-slinging)
- Sources / Further Reading
- Call to Action
Poly vs OpenClaw (Clawdbot/Moltbot): Why Production-Grade Agentic Ops Requires Governance (v3 — sources updated)
 Figure 1: Agentic systems in production need a control room mindset: governance controls + audit trail, not just “a clever agent.”
Figure 1: Agentic systems in production need a control room mindset: governance controls + audit trail, not just “a clever agent.”
TL;DR
- OpenClaw (previously branded as Clawdbot and Moltbot) is the newest “agent that does things” story making the rounds—and it’s generating attention and concern.
- The recurring theme in coverage is security risk: an autonomous agent with broad permissions is a high-blast-radius system if deployed casually.
- The second problem is deployability: even when powerful, self-hosted agent stacks often require real DevOps/security maturity to run safely.
- Poly’s advantage is that the “agentic capabilities” are already deployed inside a governed execution system: digital workers are tied to an operating graph, have outcome ownership, and run with traceability and control.
---\n
Table of Contents
- What’s happening and why this matters
- What OpenClaw is (and why it’s going viral)
- The two failure modes: security + deployability
- Why this is predictable: “agentic” expands blast radius
- How Poly positions against this category
- A practical security/ops checklist (non-theoretical)
- Field-ready messaging (no mud-slinging)
- Sources / Further Reading
---\n
What’s happening and why this matters
In the last few days, OpenClaw (and its earlier names, Clawdbot and Moltbot) has shown up in mainstream coverage and security press.
This matters for Poly for a simple reason:
Prospects will see “AI agent that runs your computer” headlines and ask whether Poly is the same category—and whether it’s safe.
The right response is not to dunk on a newcomer.
The right response is to clarify what makes agentic systems safe in production:
- governance
- least-privilege access
- audit trails
- controlled deployment
- repeatable operations
That’s the lane Poly already occupies.
---\n
What OpenClaw is (and why it’s going viral)
The story being told in headlines is:
- a personal AI agent that can operate across apps, automate tasks, and act with high autonomy
- a fast-moving project with rapid branding changes (Clawdbot → Moltbot → OpenClaw)
The more interesting signal isn’t the feature list.
It’s the reaction from the market:
- excitement (“it works!”)
- fear (“it’s a security nightmare”)
When both show up at once, it usually means the same thing:
Capability is outpacing governance.
---\n
The two failure modes: security + deployability
1) Security risk is not a “bug”—it’s a property
When an agent can:
- control a browser
- read/write files
- manage credentials
- operate unattended
…you’ve created a system with a large blast radius.
Multiple outlets have framed OpenClaw/Moltbot/Clawdbot as a security concern and have advised caution.
 Figure 2: If an agent can touch credentials, the default outcome without governance is a bigger blast radius. The problem is structural, not “a bug.”
Figure 2: If an agent can touch credentials, the default outcome without governance is a bigger blast radius. The problem is structural, not “a bug.”
2) Deployability: “self-hosted” is not the same as “usable”
The second failure mode is practical:
Even if an agent stack is technically impressive, it often requires:
- containerization
- secret management
- network policies
- sandboxing
- monitoring
- patching and version control
That’s a real burden for most teams.
So the product reality becomes:
- power exists
- but only a small group can safely deploy it
This creates an opening for Poly:
“You can get the agentic outcomes without becoming an AI security engineering team.”
---\n
Why this is predictable: agentic expands blast radius
Here’s the core pattern:
- Traditional automation has bounded blast radius (a Zap runs a step).
- Agentic automation has unbounded blast radius (an agent can improvise).
So safety requires a control plane.
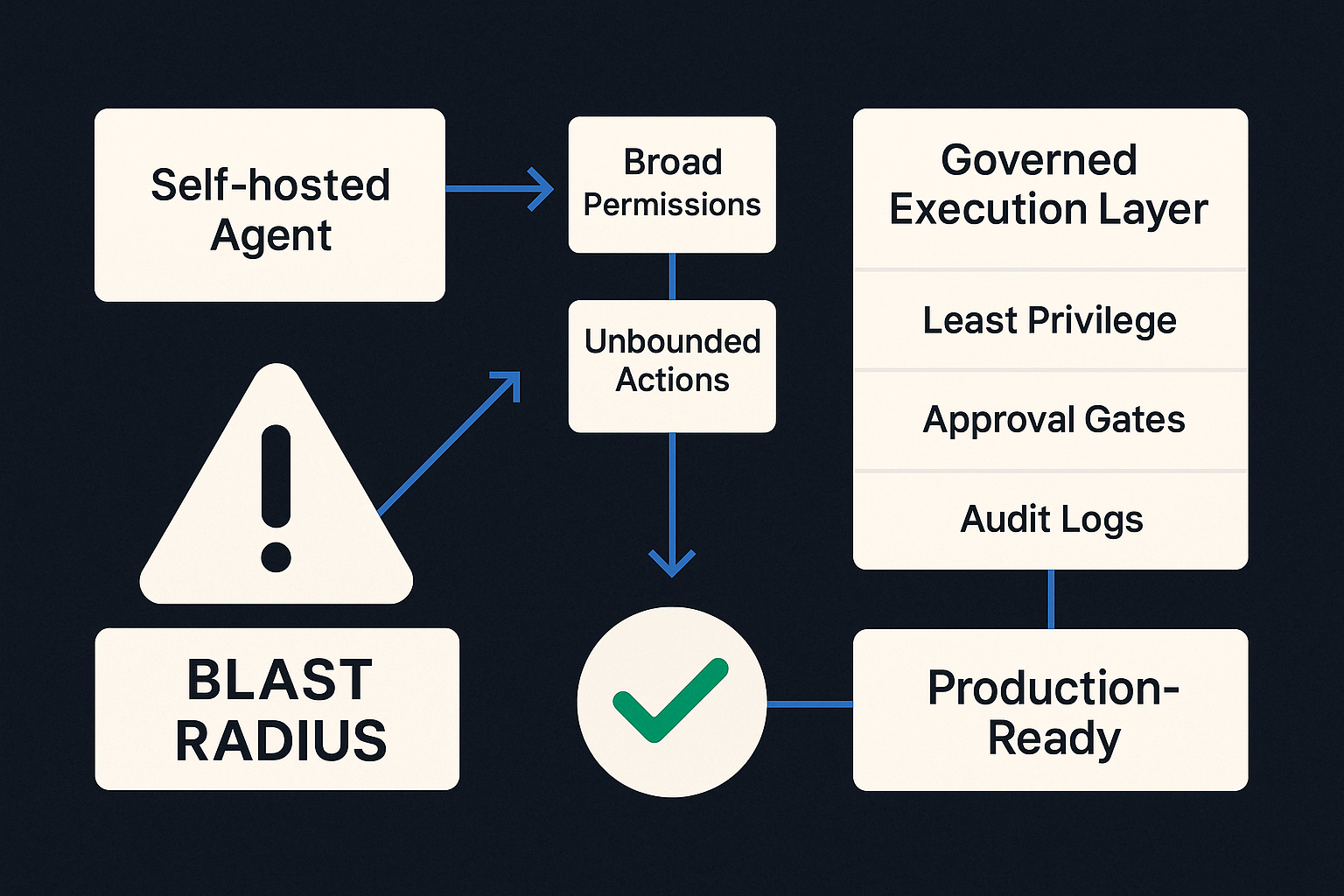 Figure 3: Two paths: “self-hosted agent + broad permissions” tends to grow blast radius; “governed execution layer” reduces it via least privilege, approval gates, and audit logs.
Figure 3: Two paths: “self-hosted agent + broad permissions” tends to grow blast radius; “governed execution layer” reduces it via least privilege, approval gates, and audit logs.
The point: the agent is not the product.
The product is whether you can:
- constrain it
- observe it
- verify outputs
- recover safely
---\n
How Poly positions against this category
Poly’s positioning in one sentence:
Poly is a governed digital workforce platform—agentic execution tied to business structure, ownership, and auditability.
Where OpenClaw-like systems often feel like:
- “a powerful agent you deploy”
Poly is:
- “a production-grade operating layer that runs digital workers safely.”
The key differentiator: already deployed + governed
Poly’s wedge is straightforward:
- you don’t just get “agent features”
- you get a system that makes those features safe to run continuously
 Figure 4: The buyer isn’t purchasing “agent capability.” They’re purchasing capability plus governance: scoped access, approvals, and observability.
Figure 4: The buyer isn’t purchasing “agent capability.” They’re purchasing capability plus governance: scoped access, approvals, and observability.
What this enables
- Repeatability: the workflow works tomorrow, not only today.
- Control: permissions and approvals aren’t an afterthought.
- Traceability: you can answer “what happened and why?”
- Outcome ownership: work has an owner and maps to KPIs.
---\n
A practical security/ops checklist (non-theoretical)
If a prospect insists on experimenting with any self-hosted agent, the pragmatic checklist is:
- Secrets management: no plaintext API keys in env files; rotate keys.
- Least privilege: scoped credentials per workflow.
- Network isolation: sandbox or egress allowlists.
- Audit logs: who/what/when for every action.
- Human-in-the-loop gates: approvals for high-risk actions.
- Versioning + patching: pin versions; update deliberately.
- Incident playbook: revoke, rotate, contain.
This is not optional if the agent can operate autonomously.
---\n
Field-ready messaging (no mud-slinging)
One-line
“OpenClaw is an exciting demo of agentic capability, but production-grade ops requires governance and deployability. Poly ships those capabilities inside a controlled operating layer.”
30-second version
“Yeah, we’ve seen the OpenClaw/Clawdbot/Moltbot buzz. It’s a good signal that agentic AI is becoming real. The issue is: when an agent has broad access, security and deployment become the whole game. Poly is built for that reality: governed execution, least-privilege workflows, auditability, and repeatable outcomes—already deployed inside the platform.”
---\n
Sources / Further Reading
- OpenClaw is a security nightmare — 5 red flags you shouldn’t ignore — ZDNET’s warning-style roundup of practical failure modes (exposure, secrets leakage, prompt injection).
- Moltbot gets another new name, OpenClaw, and triggers security fears and scams — Forbes coverage of the rapid rebrand cycle + the security backlash.
- OpenClaw AI runs wild in business environments — Dark Reading’s enterprise/security framing of privileged agents in production contexts.
- OpenClaw proves agentic AI works. It also proves your security… — VentureBeat’s CISO-oriented threat-model framing for agentic systems.
- Introducing Moltworker: a self-hosted personal AI agent, minus the minis — Cloudflare’s reference architecture for running Moltbot/OpenClaw inside isolated infrastructure primitives.
- Clawdbot (Moltbot): When “Easy AI” becomes a security nightmare — Intruder’s vulnerability-scanner vendor perspective on common misconfigurations and exposures.
- What security teams need to know about OpenClaw, the AI super agent — CrowdStrike’s defensive checklist framing (where it’s deployed, exposure, mitigation posture).
- Clawdbot: how to mitigate agentic AI security vulnerabilities — Tenable’s hardening guidance and vulnerability discussion.
- Moltbot security alert: exposed Clawdbot control panels risk credential leaks and account takeovers — Bitdefender’s reporting on exposed admin/control surfaces and credential risks.
- OpenClaw and Moltbook have security researchers worried — Mainstream summary of researcher concern around agent access + exposed deployments.
---\n
Call to Action
Deploy governed, production-ready AI workers today.
- Book a call: https://cal.com/princepspolycap/poly-digital-workforce
- Learn more: https://www.poly186.com
